Test
This is the project page of an example project. Start the page with a short description what this is about. The structure below is just a suggestion - use your judgement how you want to present your project. Also, feel free to generate additional pages if this page gets too busy.
Team members
Idea
The aim of the project is to investigate the mechanism behind RFID technology that we may or may not have taken for granted.
Background
Radio-frequency (RF) is a part of the electromagnetic spectrum typically in the range from 10kHz to 300GHz (cite). RF technology is an integral part of our everyday lives. Common examples include phone signals, radio broadcast, ID cards used for various public transport and access control (RFID), various forms of wireless payments which we know as NFC (Near Field Communication). More niche applications of RF would be control electronics, modulation of electro-optical components, ion traps etc.
In the case of RFIDs, there is usually an emitter and receiver. The emitter is usually connected to a power source and is constantly emitting a RF signal. This is known as an active component. The receiver on the other hand only has doesnt have a power supply and is usually powered by the RF wave produced by the emitter. It is also known as a passive component. In the receiver, there is also a microchip which stores data which can be extracted and transmitted through these RF waves back to the emitter to trigger certain actions.
Because most of the information transfer happens in the form of an EM wave, it can be transmitted through free space which removes the need for a physical electrical connection between users and hence the term 'Wireless'. However, just like how physical wired connections could be tapped to steal information or to manipulate data stored, such wireless technology is also susceptible to tampering.
To combat this, developments have been made to protect us from such tampering and the solution is to develop shields around the devices that prevent external EM waves from communicating with the device in the case of passive components.
Theory
Setup
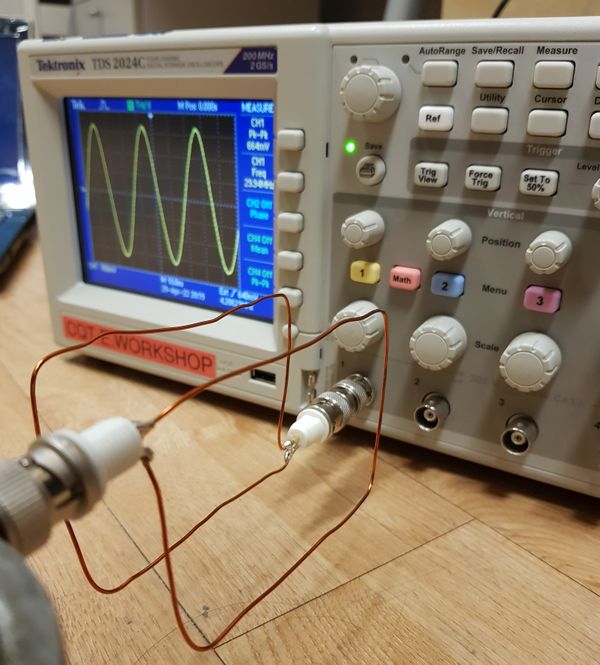
The experimental setup will aim to emulate and emitter and receiver, similar to a typical scenario in RFID systems. On the emitter side, the loop of wire is connected to a function generator (Tektronix AFG 3102) while the receiver side is connected to the oscilloscope (Tektronix TDS2024C). A gap is left between the emitter and receiver to put in a 'shield' to observe the resulting attentuation on the receiver. In such a setup, the RF waves are generated from the emitter coil and picked up by the receiver coil which is displayed on the oscilloscope. The peak to peak voltage of the signal is taken as a metric to measure the signal strength picked up by the receiver.
I will randomly type something here to check formatting.

I will randomly type something here to check formatting. I may need a longer line of text blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah
Simulated Emitter
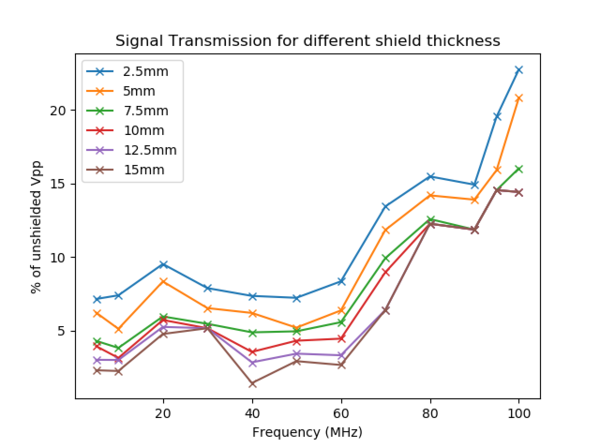
One of the properties that we might think of intuitively when it comes to shielding is the thickness. Here, we vary the thickness a metal plate between both the loops of wire for a range of frequencies available from the function generator.
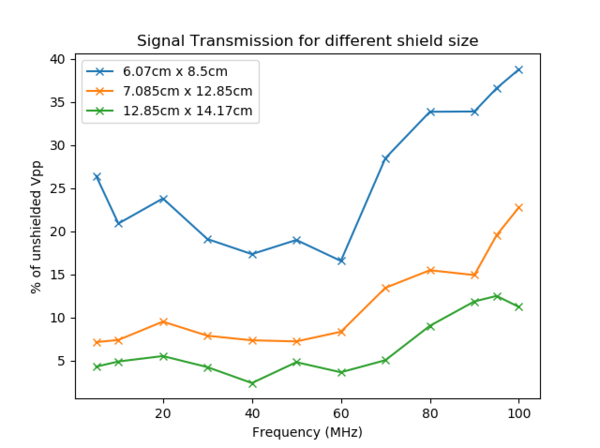
Another property which we can think of is the size (surface area) of the shield. Similarly, we recorded the signal strength in the oscilloscope for a few sizes of the shield to observe the overall effectiveness for various frequencies.
Actual Emitter
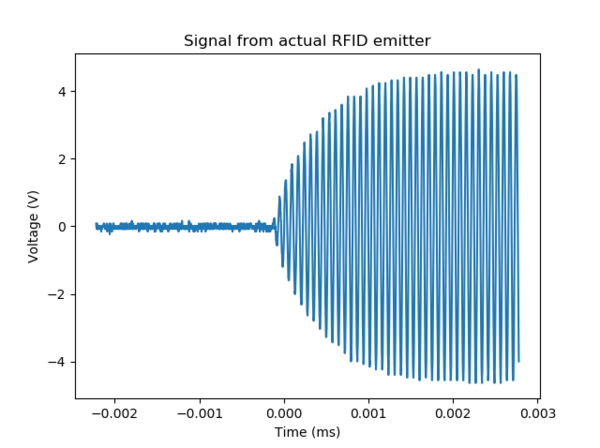
After testing with a simulated emitter, we then move on to a real life scenario with actual RFID emitter to test the conditions in which we can shield the actual passive component. To prevent the data from being misused maliciously, we will omit any specific details of the emitter. Firstly, we will look at the emitted signal from the actual emitter along with a shielding plate roughly the size of the receiver
Next, we see how the emitted signal is influenced when there is a shield plate present. When the shield plate was between the emitter and receiver, there is no signal picked up by the receiver which indicates that the design of the emitter is not a simple one as simulated in the previous section. Further investigations in that aspect could be done to determine why that is the case. Therefore there is only meaningful information when the receiver is between the shield plate and the emitter. The receiver was kept almost in contact with the emitter while distance of the shield plate to the receiver is varied.
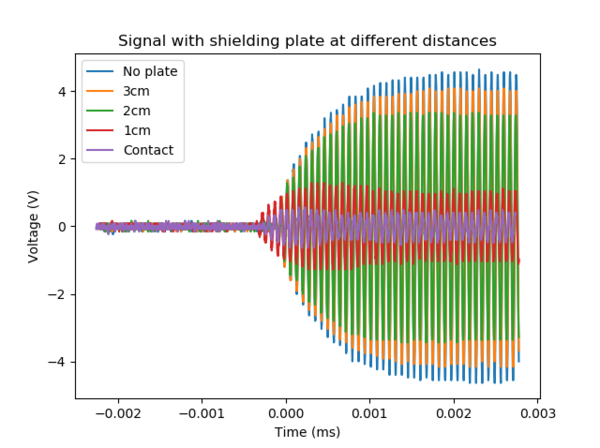
We could see that even if the plate is not between the receiver and emitter, the signal picked up is also reduced to some extent, providing a shield for the receiver.
In some cases, there were advice given to not use multiple cards on a emitter. Out of curiosity, we test the receiver along with an actual RFID card meant for the receiver.
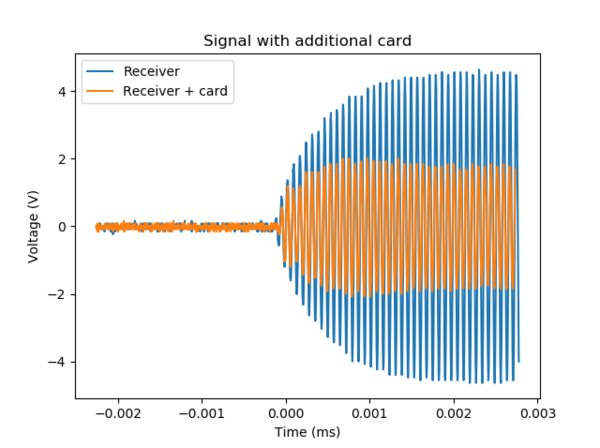
From the data, we can see that there is some attentuation due to the presence of a second card. However, it is not much and in this case, both changes to both 'cards' could have been made which is usually a non ideal outcome.
Comparison of a shielding plate to a Faraday cage
The shielding mechanism works the same way as how Faraday cages work as portrayed in some movies. However, this leads to the question of whether or not we need actual material to cover the entire surface of the plate. To put that to the test, holes were drilled into shielding plate to test the quality of shielding after reducing the amount of material in the shield. We compared 3 cases where there were no holes, 16 holes and 28 holes drilled in to the shield. Nevertheless, there were no changes to the extent of the shielding provided in both cases.


